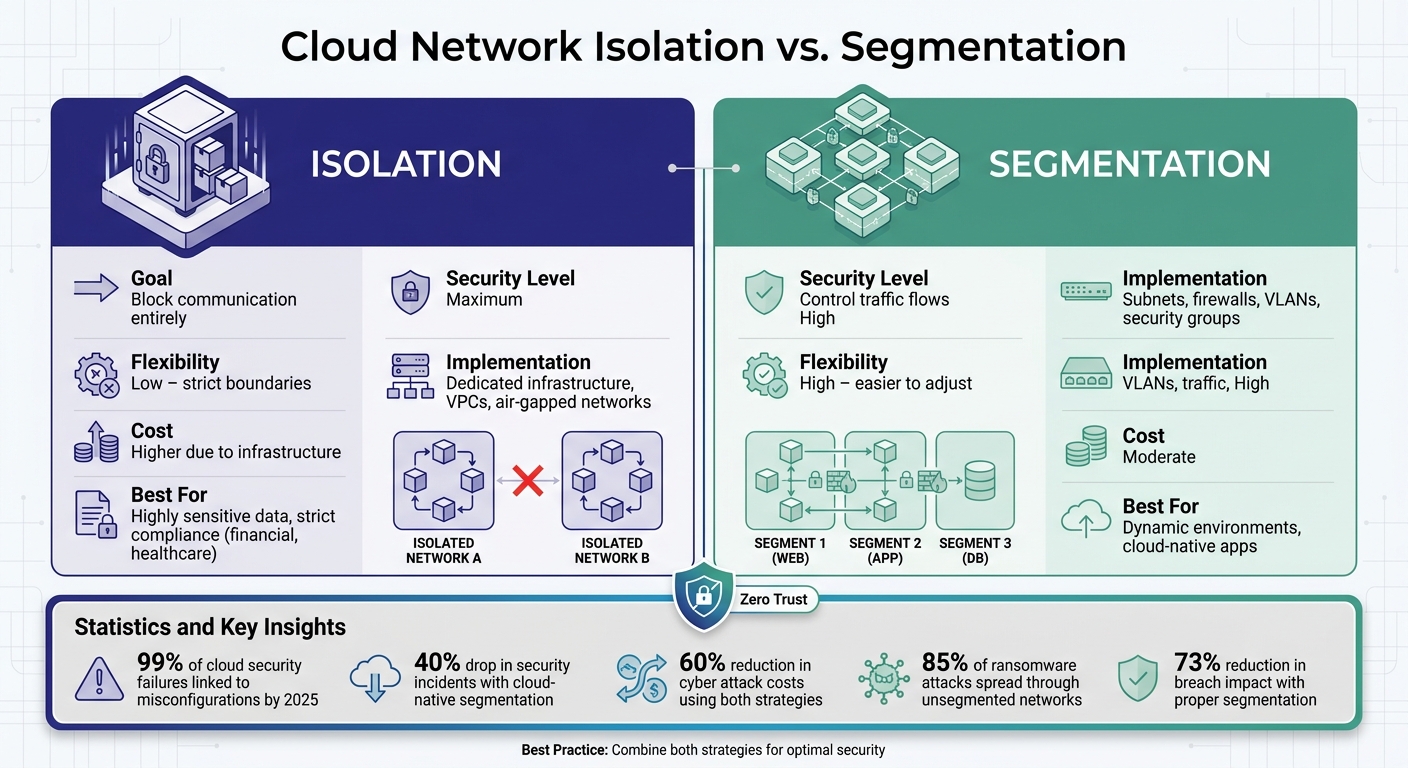
When securing cloud networks, isolation and segmentation are two key strategies you need to understand. Both aim to protect your systems but take different approaches:
- Cloud Network Segmentation: Divides a network into smaller zones (like departments in an office) to control traffic flow. It’s ideal for organizing resources and managing communication between them.
- Cloud Network Isolation: Creates strict boundaries to block communication by default, ensuring sensitive areas are completely separated. It’s designed to contain breaches and protect critical workloads.
Key Points:
- Segmentation helps reduce the impact of breaches by limiting lateral movement.
- Isolation enforces stricter separation, minimizing the risk of sensitive data being exposed.
- Both align with Zero Trust principles, requiring verification for all connections.
- Misconfigurations remain the top cause of cloud security failures - 99% by 2025.
Quick Comparison:
| Attribute | Isolation | Segmentation |
|---|---|---|
| Goal | Block communication entirely | Control traffic flows |
| Flexibility | Low – strict boundaries | High – easier to adjust |
| Security Level | Maximum | High |
| Implementation | Dedicated infrastructure, VPCs | Subnets, firewalls, VLANs |
| Cost | Higher due to infrastructure | Moderate |
When to Use:
- Choose isolation for highly sensitive data or strict compliance needs (e.g., financial or healthcare systems).
- Opt for segmentation in dynamic environments where resources need managed communication (e.g., cloud-native apps).
- Often, combining both provides the best protection.
Understanding these strategies ensures your cloud infrastructure remains secure and resilient.
Cloud Network Isolation vs Segmentation: Key Differences and Use Cases
Microsegmentation Explained (Best Practices for Cloud Security)
sbb-itb-d1a6c90
Understanding Cloud Network Segmentation
Cloud network segmentation replaces the physical barriers of traditional data centers with software-defined boundaries. Instead of using hardware like firewalls and switches, this approach relies on virtual networks, security groups, and identity-based policies to divide your environment into smaller, logical zones. These zones group resources based on their security requirements, such as separating web servers, application servers, and databases. These software-defined divisions enable the precise controls discussed in the following sections.
Definition and Key Features of Segmentation
Segmentation manages traffic by applying 5-tuple filtering, which evaluates factors like source and destination IPs, ports, and protocols. Stateful security groups act as virtual firewalls, offering fine-tuned control over resource traffic. These rules are processed in order of priority, with lower-numbered rules evaluated first. Once a match is found, traffic processing stops for that flow. Since most cloud security groups are stateful, an outbound request automatically allows the corresponding inbound response without needing a separate rule.
Subnets and VLANs organize resources by grouping them based on their function or security needs. For example, customer-facing web servers, internal application servers, and databases are typically placed in distinct subnets. Microsegmentation goes a step further by extending control to the application layer (Layer 7), enabling security at the process level rather than just the network level. This is especially useful in containerized environments where workloads are constantly shifting. These features not only enhance security but also support compliance and improve performance, as outlined in the next section.
Applications and Benefits of Segmentation
Segmentation plays a critical role in Zero Trust architectures, where every access request is verified regardless of its origin. It’s also a key strategy for achieving PCI DSS compliance, as it isolates cardholder data environments from the broader corporate network, reducing both risks and the scope of audits.
Beyond its security advantages, segmentation offers measurable business benefits. Organizations that adopt cloud-native segmentation have reported a 40% drop in security incidents compared to traditional hardware-based methods. The National Cyber Security Centre (NCSC) advises: "Segment networks to limit the impact of a compromise and use firewalls or access control lists to control traffic between segments". Additionally, segmentation reduces broadcast traffic congestion, which improves network performance - a significant advantage for environments with over 100 devices. By combining stronger security, simplified compliance, and better traffic management, segmentation has become a cornerstone of modern cloud operations.
Understanding Cloud Network Isolation
Isolation builds on segmentation by adding stricter controls to limit communication, creating an extra layer of security in your cloud environment. While segmentation organizes resources into distinct zones, isolation takes it further by separating these zones so they can't communicate by default. Think of it as locking and alarming the doors between zones to block unauthorized access. This approach enforces a "default-deny" policy at the network level, where all traffic is blocked unless explicitly allowed through specific routing rules. This sets the stage for a closer look at how isolation works and why it’s essential.
The concept of isolation is rooted in the "assume breach" philosophy. Even if application settings become overly permissive, the network layer acts as a safeguard, stopping unauthorized movement between zones. As one expert puts it:
"Network isolation is a foundational strategy for preventing lateral movement and protecting sensitive workloads".
This layered defense is especially important given the rising threat landscape. Studies show that 99% of cloud security failures are linked to customer misconfigurations, often involving poorly defined network boundaries.
Definition and Key Features of Isolation
Cloud network isolation can be implemented in two main ways: physically or logically. Physical isolation involves dedicated hardware and air-gapped networks, often seen in government or military settings. Logical isolation, more common in shared infrastructures, uses tools like Virtual Private Clouds (VPCs), Virtual Networks (VNets), and hypervisor-based separation.
Modern isolation techniques create micro-perimeters around critical workloads, aligning with Zero Trust principles that require verification for every access attempt. At the compute layer, Type 1 hypervisors play a key role by dividing physical servers into virtual machines (VMs). These hypervisors use a "Root VM" to enforce strict separation, ensuring that guest VMs can't access the host system or other VMs. For AI workloads, isolation separates the inference plane (handling API calls) from the data plane (storing training data), reducing the risk of sensitive data being intercepted. Microsoft Azure even offers "Isolated VM sizes", which dedicate hardware to a single customer to meet stringent compliance needs. Additionally, all data stored in Azure is encrypted using FIPS 140-validated 256-bit AES encryption.
Applications and Benefits of Isolation
While segmentation primarily organizes traffic, isolation is designed to minimize the impact of breaches. For instance, if a public-facing server is compromised, isolation ensures that attackers can't access backend databases or other sensitive areas. This strategy has proven effective - organizations using both segmentation and isolation have seen a 60% reduction in cyber attack costs.
Isolation isn't just about security; it also helps meet compliance standards like PCI DSS, HIPAA, and GDPR. For AI systems, private endpoints such as AWS PrivateLink or Azure Private Link ensure that sensitive traffic stays off the public internet. However, public endpoints must be explicitly disabled to avoid unsecured failover risks. Isolation also acts as a quarantine tool, allowing teams to contain compromised segments quickly and prevent further damage. As Microsoft emphasizes:
"Isolating networks is no longer optional - it is a necessary control for safeguarding cloud and hybrid environments".
Key Differences Between Isolation and Segmentation
When it comes to securing cloud networks, isolation and segmentation take very different approaches. Segmentation works by dividing a network into zones, controlling how traffic flows between them. This method allows monitored communication based on predefined security policies. On the other hand, isolation focuses on completely separating resources, blocking communication by default unless explicitly allowed through specific routing rules.
Segmentation stands out for its flexibility. It lets you adjust access controls as your business evolves - firewall rules and policies can be updated through software without requiring major infrastructure changes. In contrast, isolation often involves dedicated infrastructure or strict virtualization, which can drive up costs but ensures a higher level of security. As Zero Networks puts it:
"The defining question for security leaders in 2026 is not whether a breach will occur – it's how far the impact will spread once attackers get inside".
This distinction holds weight when you consider that 71% of enterprise risk stems from just four protocols: SMB, RDP, WinRM, and RPC. Segmentation is ideal for monitoring and filtering this kind of traffic. Isolation, however, can block it entirely for your most sensitive systems. The choice boils down to your priorities: opt for segmentation if you need managed communication or isolation for absolute separation.
Comparison Table: Isolation vs. Segmentation
| Attribute | Isolation | Segmentation |
|---|---|---|
| Primary Goal | Complete separation to prevent communication | Controlled traffic flow and reduced blast radius |
| Granularity | Coarse (entire VPC) or fine (air-gapped workload) | Zone-based or workload-based (microsegmentation) |
| Implementation | Air-gaps, dedicated hardware, VPCs, or strict hypervisors | VLANs, subnets, firewalls, and access control lists |
| Traffic Control | Blocks communication by default (deny-all approach) | Filters and monitors traffic based on policies |
| Flexibility | Low – difficult to reconfigure due to strict boundaries | High – easier to adapt to changing business needs |
| Resource Overhead | High – requires dedicated infrastructure | Moderate – involves management complexity and potential latency |
| Security Level | Maximum – significantly reduces the attack surface | High – limits lateral movement and contains breaches |
These comparisons highlight the strengths and trade-offs of each approach, helping you determine which strategy aligns best with your security objectives and operational requirements.
When to Choose Isolation or Segmentation
Factors to Consider When Choosing
Deciding between isolation and segmentation depends on several key factors, including data sensitivity, regulatory requirements, and the complexity of your infrastructure. If you're handling highly sensitive data, like financial records or medical information, isolation offers the strongest protection by completely separating secure areas from less secure ones. Industries governed by strict regulations, such as PCI DSS, HIPAA, or GDPR, often mandate segmentation to ensure sensitive environments are properly separated.
The size and complexity of your network also play a big role. Large, interconnected systems can benefit from segmentation, as it breaks the network into smaller, more manageable parts. However, this approach requires careful management to avoid the challenges of maintaining complex routing tables and firewall rules. Performance is another key consideration. While segmentation can help reduce network congestion, it may also introduce latency when traffic passes through firewalls or undergoes deep packet inspection. Still, it remains an effective way to limit lateral movement during cyberattacks.
Recommendations for Different Scenarios
Here are some recommendations to help you decide which approach works best for your specific needs. Consider your security priorities and operational goals when making this choice.
For systems requiring the highest level of protection - like industrial control systems or core financial databases - opt for physical or strict logical isolation. While this may increase administrative complexity, it minimizes the risks associated with a potential breach.
On the other hand, segmentation works well for dynamic, scalable environments, such as cloud-native applications. Tools like software-defined networking (SDN) and microsegmentation allow security policies to scale automatically as new instances are added. This is especially useful for applications that need frequent integration and low-latency communication. Private cloud models that use segmentation with fixed hardware allocation can also save between 30% and 60% compared to public cloud models with variable egress fees.
In many cases, the best solution combines both strategies. For example, you can use isolation for administrative separation by deploying dedicated Virtual Cloud Networks (VCNs) or compartments. This ensures that network administrators in one business unit cannot access or misconfigure resources in another. Within these isolated environments, segmentation can then manage traffic flow between workloads. Regardless of the approach, adopting a Zero Trust model - where every access request requires authentication and verification - is essential. Automation tools like Ansible or Terraform can further streamline policy enforcement and reduce the risk of manual errors.
Conclusion
Cloud network isolation and segmentation aren't rivals - they're partners in creating a solid security framework. Together, they help reduce the risk of lateral movement and minimize the chances of breaches. The numbers speak for themselves: 85% of ransomware attacks spread through lateral movement on flat, unsegmented networks, while proper segmentation can cut the impact of data breaches by 73%.
Choosing between these strategies depends on your organization's needs. For instance, high-sensitivity workloads, such as financial databases or AI training models, demand strict isolation. On the other hand, dynamic cloud-native applications thrive with flexible segmentation. In reality, combining both is often the most effective approach - using isolation to protect sensitive environments and segmentation to regulate traffic within those environments.
However, misconfigurations remain the Achilles' heel of cloud security. A staggering 99% of cloud security incidents will result from customer errors through 2025. This underscores the importance of proper implementation. Understanding your data flows, automating enforcement, and conducting regular audits are critical steps to avoid configuration drift. Organizations that take these precautions often experience fewer security incidents and lower breach costs.
Isolation and segmentation are also cornerstones of the Zero Trust model, which operates on the principle of verifying every access request. As cloud setups become more intricate - particularly with AI workloads requiring specialized isolation - precise configurations are essential. This integrated approach isn't just smart; it's necessary to navigate today's evolving threat landscape.
FAQs
How do I decide what needs isolation vs. segmentation?
When deciding between isolation and segmentation, it all comes down to your security priorities and the specific risks tied to your cloud environment.
- Segmentation: This approach divides your network into smaller, manageable zones. It’s a way to limit how far threats can move laterally within your system. For example, you can separate production environments from development areas, giving you more precise control over security.
- Isolation: If you’re handling highly sensitive workloads or need to meet strict compliance requirements, isolation might be the better choice. It involves creating entirely separate networks to keep critical assets secure.
To determine the best fit, consider factors like how sensitive your assets are, the potential impact of a breach, and the operational needs of your setup. Automation tools can also play a key role in applying these strategies consistently, especially in dynamic cloud environments.
What’s the simplest way to start without breaking app connectivity?
To start cloud network segmentation smoothly without affecting app connectivity, focus on controlled, step-by-step adjustments. Begin by implementing virtual network-level segmentation, like using isolated subnets or VLANs. Pair this with well-defined traffic policies, leveraging tools such as security groups or firewall rules to regulate access.
Using automation tools can make this process more efficient. These tools help ensure consistent deployment, reduce errors, and maintain seamless connectivity for legitimate traffic while scaling your network segmentation efforts.
How can I prevent segmentation/isolation misconfigurations over time?
To prevent issues like segmentation or isolation misconfigurations, it's essential to rely on continuous monitoring and automation. Regular audits and validations of segmentation policies ensure they align with your security requirements. By automating rule management, you can reduce human error and keep up with dynamic environments.
Incorporating a Zero Trust approach - which focuses on least privilege access and ongoing validation - adds another layer of protection. Additionally, keeping controls up-to-date and testing them frequently helps tackle emerging threats and adapt to infrastructure changes, ultimately lowering long-term risks.

