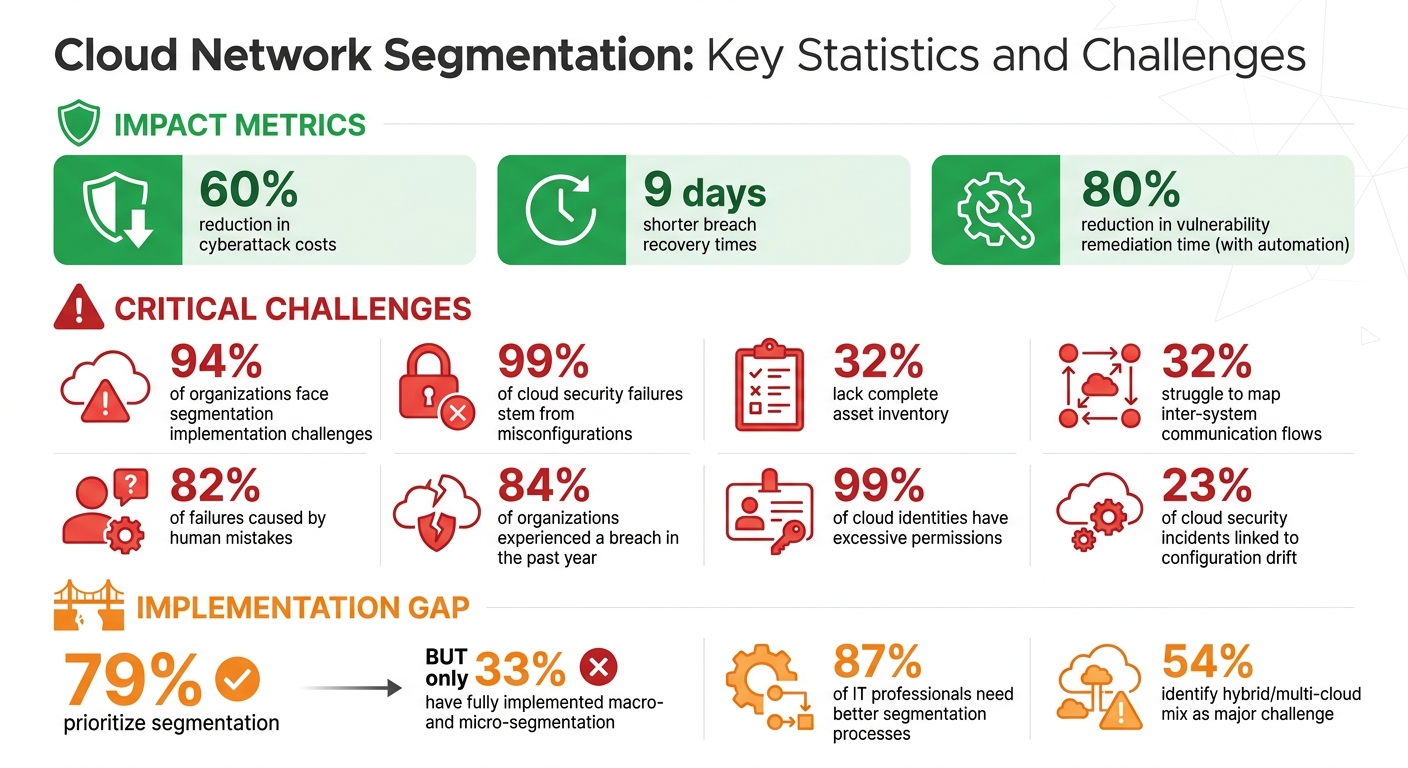
Cloud network segmentation is a method to divide cloud environments into secure zones, limiting lateral movement during breaches. This approach reduces cyberattack costs by 60% and shortens breach recovery times by 9 days. However, 94% of organizations face challenges implementing segmentation due to complex hybrid setups, visibility gaps, and configuration errors. Misconfigurations account for 99% of cloud security failures, and 82% stem from human mistakes.
Key issues include:
- Hybrid Complexity: Managing multiple platforms like AWS, Azure, and GCP increases errors.
- Visibility Gaps: 32% of organizations lack a full inventory of assets.
- Access Control Risks: Excessive permissions and configuration drift create vulnerabilities.
- Performance and Compliance: Segmentation can slow networks and complicate regulatory adherence.
Solutions include adopting zero-trust models, automating segmentation with Cloud-Native Application Protection Platforms (CNAPPs), and conducting regular audits. Automation has reduced vulnerability remediation time by up to 80% for some businesses, proving its effectiveness in addressing these challenges.
Cloud Network Segmentation: Key Statistics and Challenges
Main Security Challenges in Cloud Network Segmentation
Complexity in Hybrid and Multi-Cloud Environments
Managing security in a hybrid IT setup combining cloud platforms, containers, and legacy systems is no small feat. In fact, 54% of organizations identify this mix as a major challenge. Each cloud provider - AWS with IAM, Azure with RBAC, and GCP with its resource hierarchy - demands unique configurations. This variety increases the chances of mistakes, especially when security teams have to manually translate the same segmentation policies across multiple platforms.
Dynamic scaling adds another layer of difficulty. Static security measures struggle to keep up without automation, making it harder to maintain consistent protection. On top of that, limited visibility into assets makes these tasks even more daunting, leaving room for potential errors.
Lack of Asset Visibility and Discovery
Visibility issues are another significant hurdle for effective segmentation. 32% of organizations admit they don’t have a complete inventory of their assets across distributed environments. Without knowing what’s out there, it becomes nearly impossible to differentiate between normal activity and suspicious behavior. Similarly, 32% of companies struggle to map legitimate inter-system communication flows.
Aamer Akhter, Senior Director of Product Management at Cisco, sums it up well:
"You can't secure what you don't know about."
This lack of visibility can lead to critical oversights, such as failing to notice an internal system attempting unauthorized internet access. As organizations evolve, legacy systems often fall off the radar, leaving security teams hesitant to enforce controls on unfamiliar applications. The fear of disrupting critical operations only adds to the challenge, making it harder to apply proper access restrictions.
Access Control and Misconfiguration Risks
Misconfigurations are a persistent problem in cloud security. Gartner estimates that up to 99% of cloud security failures through 2025 will stem from configuration errors, with 82% caused by human mistakes. Common issues like excessive permissions, open SSH/RDP ports, and hardcoded API keys create easy entry points for attackers. Configuration drift - when settings unintentionally change over time - has been linked to 23% of cloud security incidents.
Shockingly, 99% of cloud users, roles, services, and resources are granted more permissions than they actually need. For example, a reporting application might be given full "Write" access when it only requires "Read" privileges. These unnecessary permissions can become serious vulnerabilities if exploited. Misconfigurations don’t just increase the risk of breaches - they also weaken efforts to limit lateral movement during an attack. With 84% of organizations having experienced a breach in the past year, these errors aren’t just theoretical - they’re a direct path to security incidents.
sbb-itb-d1a6c90
Operational Challenges in Cloud Network Segmentation
Performance Overhead and Management Burden
While segmentation enhances security, it can come at the cost of performance. Traffic moving between segments often passes through firewalls, which can introduce latency. Additionally, processes like deep packet inspection (DPI) require significant processing power, potentially slowing down the network compared to unsegmented setups.
Managing segmentation adds another layer of complexity. A striking 87% of IT professionals highlight the need for better segmentation processes. As applications evolve, security teams must continuously adjust policies and monitor connectivity. This challenge is even greater with microsegmentation, where policies are applied at the workload level. Tools like Cilium and NSX can help, but they demand specialized expertise.
On the upside, effective segmentation can prevent resource contention. By isolating traffic, it ensures that unrelated workloads don’t compete for bandwidth, reducing congestion. However, achieving this balance between security and efficiency requires strategies such as:
- Link aggregation (LACP): Boosts bandwidth to handle traffic demands.
- VLAN trunking: Cuts down on physical hardware needs.
- Automation tools: Solutions like Ansible or Terraform simplify configuration management and ensure consistency.
These operational hurdles make it even harder to meet compliance requirements.
Compliance and Validation Gaps
Beyond performance and management, regulatory compliance is another major challenge. Despite 79% of organizations prioritizing segmentation, only 33% have fully implemented both macro- and micro-segmentation. Keeping policies consistent across multiple cloud environments is difficult, especially when traditional validation methods are too resource-intensive.
Cloud abstraction layers often obscure visibility, making it hard to confirm whether segmentation policies are functioning as intended. Manual audits and scans struggle to keep up with the fast pace of cloud changes, leaving organizations uncertain about their security posture. Shadow IT - unsanctioned cloud resources - further complicates matters, creating blind spots where policies can’t be enforced or audited. Gartner predicts that 99% of cloud security failures through 2025 will stem from customer missteps, emphasizing how critical it is to address configuration and validation gaps.
A shift from periodic manual reviews to continuous automated validation is essential. Real-time monitoring can catch misconfigurations immediately, while regular penetration testing ensures critical segments remain secure. As noted in the 2025 Cisco Segmentation Report:
"If I could change one thing about my organization's segmentation approach, it would definitely be to further automate and integrate our segmentation tools and processes".
Automation not only improves efficiency but also ensures compliance with standards like PCI DSS or HIPAA, even in rapidly evolving cloud environments.
Research-Based Strategies to Address Challenges
Zero-Trust Security Models
Zero-trust architecture operates on a simple but powerful idea: trust no one by default. Instead of assuming that users or systems within a network are safe, it scrutinizes every access request. This principle has gained traction, with 90% of IT and security professionals rating zero-trust as "very" or "extremely" important for strengthening security measures. The urgency is clear - attackers can now move from gaining initial access to stealing data in just 72 minutes, a significant acceleration compared to 2025. This makes the old "trust but verify" approach obsolete.
A key component of zero-trust is microsegmentation, which isolates individual workloads and user identities. By doing so, it hides them from unauthorized users and confines attackers to a single segment, limiting potential damage. The principle of least privilege further reduces risks by ensuring users and devices can only access the resources they absolutely need. However, effective implementation requires careful preparation - mapping application dependencies and traffic patterns is essential for crafting strong security policies. Adding Just-in-Time (JIT) privileged access, which provides elevated permissions only when necessary and requires multi-factor authentication, adds an extra layer of security.
To complement these measures, automated tools can simplify and enhance the process of dynamic segmentation.
Automation and Cloud-Native Application Protection Platforms (CNAPPs)
Manual segmentation often struggles to keep up with the fast-moving nature of cloud environments. Enter Cloud-Native Application Protection Platforms (CNAPPs), which combine various security functions - like cloud security posture management, workload protection, and entitlement management - into a single, unified tool.
The benefits of automation are clear. In 2026, Vikram Moole, Security and Compliance Manager at Bidgely, noted that using PingSafe (SentinelOne) cut vulnerability remediation time by 70%–80%. Similarly, Pedro Leão from Orbcom, Lda. reduced manual review times by 20%–25% with Check Point CloudGuard CNAPP. Another mid-size software company improved its CIS benchmark compliance score from 72% to 92% within just three months of adopting CNAPP.
Automation doesn't stop there. Tag-based policies allow security rules to adapt as workloads grow, ensuring new resources are segmented correctly without human intervention. Embedding automated security scans into CI/CD pipelines helps catch infrastructure-as-code misconfigurations before they go live, addressing potential issues early on.
Regular Audits and Continuous Monitoring
Even with robust segmentation strategies, regular audits and continuous monitoring are critical. With 99% of cloud identities having excessive permissions and 82% of cyber incidents occurring without malware, monitoring is non-negotiable. The rapid pace of cloud changes often leads to configuration "drift", where unintended exposures arise.
Centralizing flow logs, audit logs, and security events into a single platform can streamline investigations, eliminating the inefficiency of switching between multiple consoles. Real-time alerts for unusual traffic patterns or unauthorized access attempts provide an additional layer of protection. Mapping data flows between services and regions is equally important to identify hidden dependencies and shadow IT workloads.
Regular penetration tests and red team exercises can uncover weaknesses in segmentation controls before attackers exploit them. These audits are more than just a best practice - they’re increasingly required by compliance frameworks like PCI DSS, HIPAA, and GDPR. Even cyber insurance providers are starting to demand them, offering lower premiums to organizations that meet these standards.
Microsegmentation Explained (Best Practices for Cloud Security)
Conclusion: Key Takeaways for Businesses
Cloud network segmentation has shifted from being a technical consideration to a core strategy for business survival. Research reveals that 84% of organizations experienced a breach in the past year, with nearly half of all cyberattacks now originating in the cloud.
This data underscores the pressing need to address complexity, visibility, and automation in cloud security. With 94% of organizations struggling with segmentation challenges, those that adopt automation and continuous monitoring will be better equipped to fend off threats. Gartner’s forecast that 99% of cloud security failures through 2025 will result from customer errors further highlights the urgency for businesses to act now.
Implementing zero-trust architectures and leveraging automation tools isn’t just about upgrading technology - it’s about ensuring operational resilience. Beyond the technical aspects, businesses must align their security measures with operational efficiency to create a more robust defense.
To complement these efforts, tools like BizBot can simplify business operations - managing everything from accounting to subscription services. By streamlining these processes, security teams can dedicate their full attention to safeguarding critical assets and maintaining customer trust. When operations are seamless, your security investments deliver even greater value.
FAQs
Where should I start with cloud segmentation in a hybrid environment?
To establish a secure and efficient hybrid cloud environment, begin by setting up clear segmentation boundaries. Use tools like virtual private clouds (VPCs), subnets, and security groups to isolate critical assets, which helps reduce potential attack surfaces.
Next, map out your network architecture to pinpoint vulnerabilities and ensure you can enforce traffic flow policies effectively. Incorporate monitoring tools to stay on top of compliance requirements and detect potential threats early.
Make sure to apply least privilege and zero-trust principles, which limit access to only what is necessary and verify every access request. Finally, document your entire strategy thoroughly - this ensures your setup remains secure and manageable over time.
How can I find hidden assets and map service-to-service traffic flows?
To uncover hidden assets and understand service-to-service traffic within a cloud environment, it's essential to use a mix of advanced strategies. Techniques like policy-based controls, virtual networks, and identity-informed policies can play a key role. Additionally, micro-segmentation is an effective way to isolate workloads, which helps minimize lateral movement if an incident occurs.
Automated tools add another layer by continuously monitoring traffic patterns. These tools not only improve visibility but also help detect hidden assets. This approach aligns with Zero Trust principles, ensuring that access is granted on a least-privilege basis, ultimately strengthening overall security.
How do I reduce misconfigurations and permission sprawl without slowing the network?
To keep misconfigurations and permission sprawl in check while maintaining network performance, rely on automation and integrated tools. Automation helps enforce consistency, closing security gaps by addressing potential issues before they escalate. Tools like AI-driven guardrails and automated policy enforcement make it easier to scale operations, cut down on manual mistakes, and uphold strong, adaptive security measures - all without sacrificing speed or adding unnecessary complexity.


