Rebalancing software is critical for managing financial data and executing transactions, but it also comes with security risks like data breaches and compliance violations. To mitigate these risks, modern efficient tools for security offer real-time monitoring, compliance automation, and AI-driven threat prioritization. This article examines three tools - Sysdig, Wazuh, and Tool C - that help secure rebalancing software by focusing on runtime protection, endpoint visibility, and threat detection.
Key Highlights:
- Sysdig: Focuses on cloud-native environments with eBPF technology for real-time system monitoring. Reduces vulnerability noise by 98% and improves response time by 76%.
- Wazuh: Open-source platform offering endpoint insights and File Integrity Monitoring. Tracks changes to rebalancing algorithms and detects suspicious activity.
- Tool C: A runtime-first module within Sysdig, leveraging AI and Falco engine for quick detection of emerging threats.
Each tool has its strengths, whether it's Sysdig’s advanced runtime insights, Wazuh’s detailed endpoint monitoring, or Tool C’s AI-driven threat response. The right choice depends on your team’s size, expertise, and security priorities.
1. Tool A
Sysdig is a cloud-native platform designed for real-time threat detection and runtime protection. By utilizing eBPF technology, it monitors Linux kernel events, offering detailed visibility into system activity, container operations, and Kubernetes environments - all while preserving application performance. For high-frequency rebalancing software, Sysdig enables security teams to track every system call, helping to prevent unauthorized changes in trade execution and portfolio data. Let’s dive into its standout security features.
Security Monitoring Features
Sysdig focuses on monitoring actual cloud activity during runtime, rather than relying on static scans. It combines posture management, vulnerability assessment, and cloud workload protection into a unified lifecycle approach. Companies using Sysdig have reported impressive results, including a 95% reduction in time spent on vulnerability management and a 98% decrease in vulnerability noise by prioritizing only active, reachable risks.
The platform’s drift detection feature plays a key role in safeguarding financial rebalancing processes. Powered by the Falco engine, it identifies unexpected behavior, configuration changes, and unauthorized attacks in real time. David Fox, CISO at Neo4j, underscores the importance of such capabilities:
Neo4j provides critical insights to organizations in some of the world's most heavily regulated industries... A security breach on their platform could have serious consequences.
Threat Detection Capabilities
Sysdig’s threat detection is impressively fast, identifying threats within just 2 seconds. This rapid detection minimizes the risk of unauthorized financial transactions. Its Agentic AI Defense adapts to specific environments, guiding security actions and reducing the Mean Time to Resolution (MTTR) by 76% - a crucial edge in protecting high-frequency financial operations. Zsolt Nemeth, CEO of R6 Security Inc, highlights its effectiveness:
Falco's threat detection and real-time alerting capabilities... help effectively address security issues that might evade other security offerings.
Compliance and Reporting Tools
Sysdig has earned accolades as a "Leader" in the 2026 Forrester Wave for CNAPP and as a "Customers' Choice" in the Gartner Peer Insights report, with 99% of customers recommending the platform. It integrates seamlessly with major cloud providers (AWS, GCP, and Azure) and SIEM platforms, streamlining compliance by automating evidence collection. For rebalancing software operating in highly regulated industries, Sysdig’s pre-configured rule sets ensure compliance with strict banking standards - without requiring manual intervention.
sbb-itb-d1a6c90
2. Tool B
Sysdig focuses on cloud-native capabilities, but Wazuh takes a different route with its open-source platform, emphasizing detailed endpoint insights. Wazuh, an open-source SIEM platform, strengthens endpoint visibility, which is key for protecting rebalancing algorithms. Instead of relying solely on log data, Wazuh uses an agent-based system to detect suspicious activity more effectively. This deeper visibility plays a critical role in preventing tampering with rebalancing algorithms.
Security Monitoring Features
Wazuh's File Integrity Monitoring keeps track of file changes, including content, permissions, ownership, and attributes. Its Security Configuration Assessment and log analysis help uncover misconfigurations and potential compromises. The platform even identifies which users or applications made specific changes - an essential feature for guarding rebalancing algorithms against interference. On top of that, Wazuh aggregates and correlates logs to detect issues like repeated login failures, providing actionable insights into potential security breaches.
Threat Detection Capabilities
Thanks to its agent-based setup, Wazuh delivers real-time threat detection by continuously monitoring endpoints. This level of monitoring adds a layer of protection and sets a strong foundation for comparing other tools in the analysis.
3. Tool C
Tool C, a sophisticated module within Sysdig, takes a different approach by focusing on runtime-first security in cloud-native environments. Unlike the endpoint-focused strategies of Tool B, Tool C uses real-time runtime analysis to address threats as they unfold. Instead of relying solely on static configurations, it employs eBPF technology to actively monitor system activity in real time, providing an additional layer of defense against emerging threats.
Security Monitoring Features
Tool C introduces Runtime Insights, which emphasize real-time responses over static alerts. Its Agentic AI adapts to the specific nuances of your environment, encouraging timely security actions rather than overwhelming users with excessive notifications. This tool integrates posture management, vulnerability scanning, and workload protection into one comprehensive CNAPP solution.
Threat Detection Capabilities
Powered by Falco's open-source engine, Tool C offers deep runtime visibility, allowing for quick detection of unauthorized processes or configuration changes from a runtime-first perspective. Its AI-driven capabilities significantly reduce Mean Time to Repair (MTTR) by an impressive 76%. Forrester recognized Sysdig as a "Leader in CNAPP" in 2026, with 99% of users recommending the platform for cloud-native security. These runtime-focused features highlight Tool C's ability to address modern security challenges effectively while balancing its benefits and trade-offs.
Advantages and Disadvantages
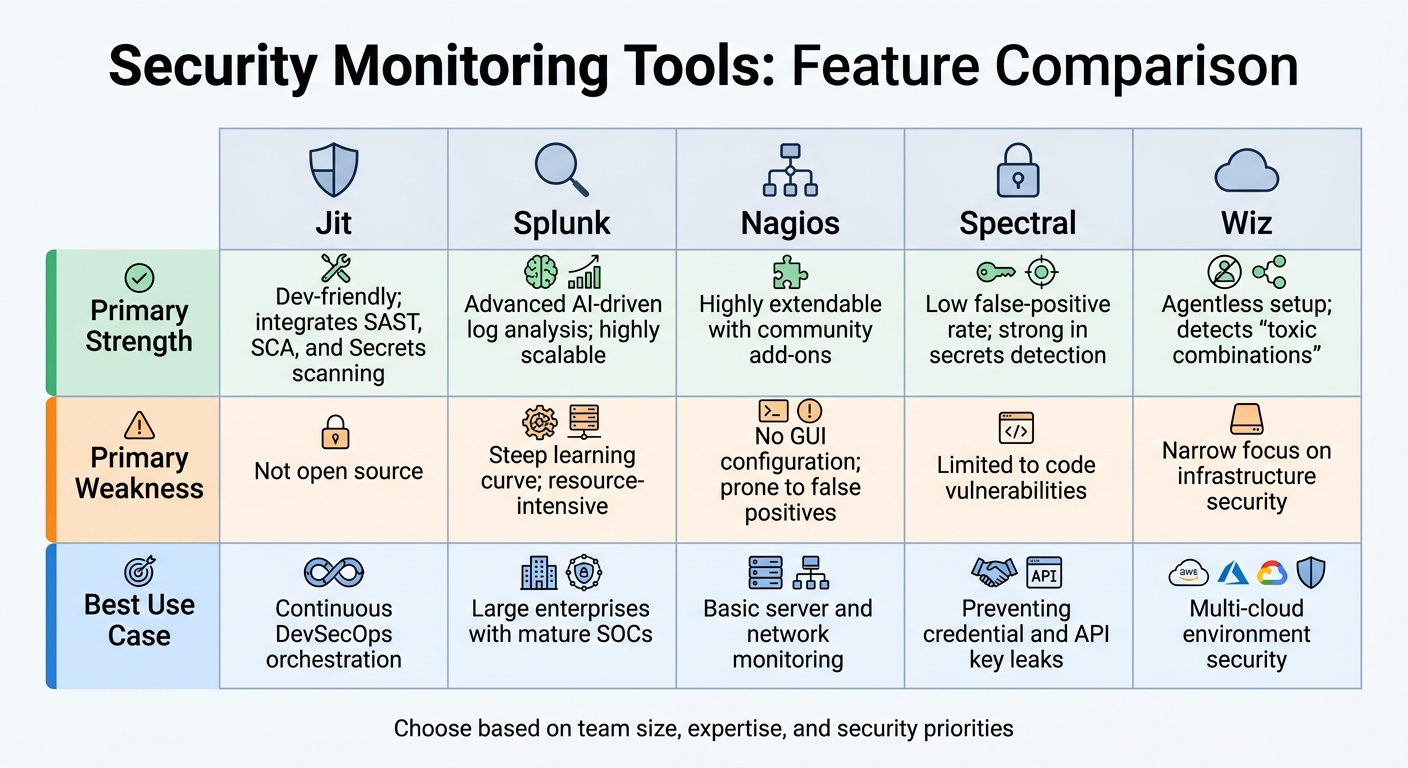
Security Monitoring Tools Comparison: Strengths, Weaknesses, and Best Use Cases
Security monitoring tools bring a mix of strengths and challenges, especially when it comes to rebalancing software. Developer-focused platforms like Jit and Spectral are great for identifying vulnerabilities early in the development process with minimal setup. On the other hand, enterprise solutions like Splunk excel in advanced log analysis but demand a high level of technical expertise. As Jeff Haynie, CTO at ShopMonkey, explained:
Jit provides continuous security by enabling my team to find and fix vulnerabilities in-PRs without slowing them down or expecting them to be security experts.
The key is finding the right balance between usability and control. For instance, Nagios is a popular choice for server monitoring because of its open-source flexibility and extensive community add-ons. However, its outdated interface and lack of GUI configuration can make it difficult to navigate. Meanwhile, cloud-native tools like Wiz leverage agentless scanning, making them ideal for large-scale, multi-cloud deployments. But they come with trade-offs, such as focusing more on infrastructure than the entire software development lifecycle. Similarly, Splunk’s robust capabilities often come at the cost of heavy resource usage, which can strain systems.
Here’s a quick breakdown of the tools, their strengths, weaknesses, and ideal use cases:
| Tool | Primary Strength | Primary Weakness | Best Use Case |
|---|---|---|---|
| Jit | Dev-friendly; integrates SAST, SCA, and Secrets scanning | Not open source | Continuous DevSecOps orchestration |
| Splunk | Advanced AI-driven log analysis; highly scalable | Steep learning curve; resource-intensive | Large enterprises with mature SOCs |
| Nagios | Highly extendable with community add-ons | No GUI configuration; prone to false positives | Basic server and network monitoring |
| Spectral | Low false-positive rate; strong in secrets detection | Limited to code vulnerabilities | Preventing credential and API key leaks |
| Wiz | Agentless setup; detects "toxic combinations" | Narrow focus on infrastructure security | Multi-cloud environment security |
When selecting a tool for rebalancing software, it’s crucial to match the tool’s capabilities with the team’s scale and expertise.
Nimrod Peretz, VP R&D at Wobi, emphasized the value of accuracy:
One of the reasons we picked Spectral over the other products is Spectral has low false-positive results, which give us a high confidence factor and save us precious development time.
Beyond these tools, others like Sysdig, Wazuh, and Tool C offer strong runtime and endpoint monitoring. Meanwhile, solutions like Apiiro focus on identifying significant changes in software architecture, providing insights into emerging risks. Smaller teams often benefit most from tools with built-in automation, while larger enterprises with dedicated Security Operations Centers should opt for platforms that can be customized and assign risk ownership directly to the developers responsible for fixing issues.
Conclusion
Choosing the right security tool comes down to your team's structure, workflows, and risk priorities. Each tool has its strengths, and the best fit depends on the specific needs of your organization.
For development teams working on custom platforms, Semgrep stands out. Its AI-assisted remediation reduces false positives for high-severity issues by 98% and cuts triage workloads by 80% - a game-changer for teams balancing security with fast-paced development cycles.
If you're looking for a cost-effective and comprehensive monitoring solution, Wazuh is a strong contender. As an open-source unified SIEM and XDR platform, it delivers robust infrastructure monitoring. However, keep in mind that it may require more setup compared to cloud-native SaaS tools.
For organizations prioritizing risk mapping and architectural insights, Apiiro and Legit Security offer tools that help teams focus on material changes rather than sifting through generic alerts.
Smaller businesses or those already using observability platforms might find Datadog to be the ideal choice. With its ability to integrate cloud security with live traffic and service data, Datadog simplifies operations for teams without dedicated security staff. It has earned a 4.4/5 rating from 1,156 users and offers a freemium model, making it accessible for budget-conscious teams. Notably, 60% of the top security monitoring tools now provide free or freemium plans.
Before committing to a solution, it's wise to run a two-week pilot program. During this trial, evaluate not just the tool's features but also its total cost - including data fees and the labor needed for manual triage. This approach ensures you're making a well-informed decision that aligns with your team's needs and budget.
FAQs
Which tool fits a small team vs a full SOC?
For smaller teams, LiteSOC is a great option. It provides real-time threat detection with minimal setup, making it perfect for startups or developers who need quick and straightforward security insights. It’s easy to use and doesn’t demand a lot of resources.
For larger-scale operations, platforms like Panther or RADICL are better choices. These tools offer advanced AI-driven detection, automation, and investigation features, making them ideal for managing extensive security operations and addressing complex threats effectively.
How do runtime tools avoid slowing trading systems?
Runtime tools help keep trading systems running smoothly by spotting problems as they happen. They use methods like monitoring system calls and checking file integrity to detect threats quickly. This ensures issues are addressed promptly without slowing down system performance.
What should I measure in a 2-week pilot?
During a two-week pilot, assess how effectively rebalancing tools can lower risk, improve portfolio diversification, and track shifts in asset allocation over time. These factors will help gauge the tool's performance and determine if it aligns with your requirements.